Cisco Talos
Threat intelligence services allow the exchange of threat information such as vulnerabilities, indicators of compromise (IOC), and mitigation techniques. This information is not only shared with personnel, but also with security systems. As threats emerge, threat intelligence services create and distribute firewall rules and IOCs to the devices that have subscribed to the service.


One such service is the Cisco Talos Threat Intelligence Group, shown in the figure. Talos is one of the largest commercial threat intelligence teams in the world, and is comprised of world-class researchers, analysts and engineers. The goal of Talos is to help protect enterprise users, data, and infrastructure from active adversaries. The Talos team collects information about active, existing, and emerging threats. Talos then provides comprehensive protection against these attacks and malware to its subscribers.
Cisco Security products can use Talos threat intelligence in real time to provide fast and effective security solutions. Cisco Talos also provides free software, services, resources, and data. Talos maintains the security incident detection rule sets for the Snort.org, ClamAV, and SpamCop network security tools.
FireEye
FireEye is another security company that offers services to help enterprises secure their networks. FireEye uses a three-pronged approach combining security intelligence, security expertise, and technology.
FireEye offers SIEM and SOAR with the Helix Security Platform, which uses behavioral analysis and advanced threat detection and is supported by the FireEye Mandiant worldwide threat intelligence network. Helix is cloud-hosted security operations platform that combines diverse security tools and threat intelligence into a single platform.
The FireEye Security System blocks attacks across web and email threat vectors, and latent malware that resides on file shares. It can block advanced malware that easily bypasses traditional signature-based defenses and compromises the majority of enterprise networks. It addresses all stages of an attack lifecycle with a signature-less engine utilizing stateful attack analysis to detect zero-day threats.
Search for FireEye on the internet and view the security intelligence resources it offers.
Automated Indicator Sharing
The U.S. Department of Homeland Security (DHS) offers a free service called Automated Indicator Sharing (AIS). AIS enables the real-time exchange of cyber threat indicators (e.g., malicious IP addresses, the sender address of a phishing email, etc.) between the U.S. Federal Government and the private sector.
AIS creates an ecosystem where, as soon as a threat is recognized, it is immediately shared with the community to help them protect their networks from that particular threat.
Search the internet for “DHS AIS” service to learn more.
Common Vulnerabilities and Exposures (CVE) Database
The United States government sponsored the MITRE Corporation to create and maintain a catalog of known security threats called Common Vulnerabilities and Exposures (CVE). The CVE serves as a dictionary of common names (i.e., CVE Identifiers) for publicly known cybersecurity vulnerabilities.
The MITRE Corporation defines unique CVE Identifiers for publicly known information-security vulnerabilities to make it easier to share data.
Search the internet for “Mitre Corporation” and view information about CVE
Threat Intelligence Communication Standards
Network organizations and professionals must share information to increase knowledge about threat actors and the assets they want to access. Several intelligence sharing open standards have evolved to enable communication across multiple networking platforms. These standards enable the exchange of cyber threat intelligence (CTI) in an automated, consistent, and machine readable format.
Three common threat intelligence sharing standards include the following:
- Structured Threat Information Expression (STIX) – This is a set of specifications for exchanging cyber threat information between organizations. The Cyber Observable Expression (CybOX) standard has been incorporated into STIX.
- Trusted Automated Exchange of Indicator Information (TAXII) – This is the specification for an application layer protocol that allows the communication of CTI over HTTPS. TAXII is designed to support STIX.
- CybOX – This is a set of standardized schema for specifying, capturing, characterizing, and communicating events and properties of network operations that supports many cybersecurity functions.
These open standards provide the specifications that aid in the automated exchange of cyber threat intelligence information in a standardized format. Search the internet to learn more about STIX, TAXII, and CybOX.

The Malware Information Sharing Platform (MISP) is an open source platform for sharing indicators of compromise for newly discovered threats. MISP is supported by the European Union and is used by over 6,000 organizations globally. MISP enables automated sharing of IOCs between people and machines by using STIX and other export formats.
Threat Intelligence Platforms
As we have seen, there are many sources of threat intelligence information, each of which may have its own data format. Accessing and using multiple threat intelligence sources can be very time-consuming. To help cybersecurity personnel make the best use of threat intelligence, threat intelligence platforms (TIP) have evolved.
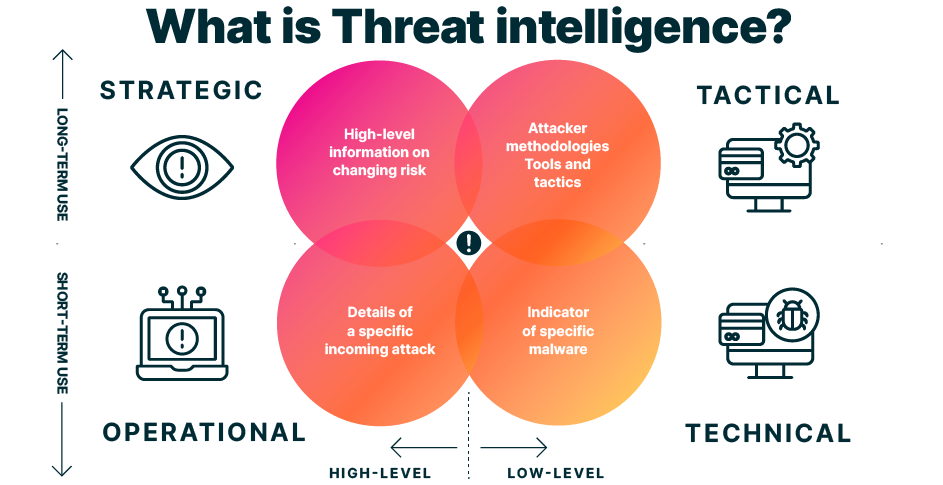
A threat intelligence platform centralizes the collection of threat data from numerous data sources and formats. There are three major types of threat intelligence data. The first is indicators of compromise (IOC). The second is tools, techniques, and procedures (TTP). The third is reputation information about internet destinations or domains. The volume of threat intelligence data can be overwhelming, so the threat intelligence platform is designed to aggregate the data in one place and–most importantly–present the data in a comprehensible and usable format.
Organizations can contribute to threat intelligence by sharing their intrusion data over the internet, typically through automation. Many threat intelligence services use subscriber data to enhance their products and to keep current with the constantly changing immerging threat landscape.
Honeypots are simulated networks or servers that are designed to attract attackers. The attack-related information gathered from honeypots can then be shared with threat intelligence platform subscribers. However, hosting honeypots can itself be a risk. Basing a honeypot in the cloud isolates the honeypot from production networks. This approach is an attractive alternative for gathering threat intelligence.
Copyrights :cisco skills for all.